To save or not to save, that is the question…
Asking around our friendship group, 80% will say that they have lost data before. Mostly private persons are affected by data loss since in the corporate environment cybersecurity officers and the GDPR decree fight fiercely with the business for creating, testing and maintaining the right data backup strategy.
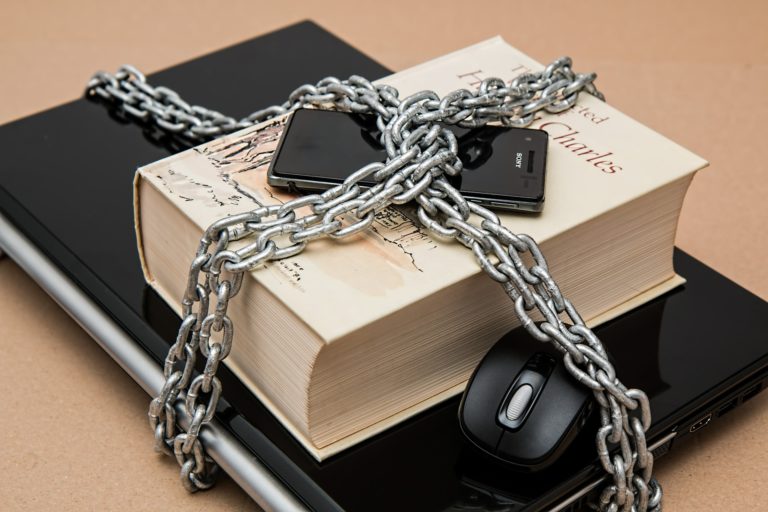
Taking the number of lost hardware (smartphones, tablets, laptops, pen drives, etc.) into account, the amount of data is even more frightening with today’s privacy approaches. The mere thought of losing private data makes every businessman shiver, so if the term ‘data protection incident’ comes up, everyone flees.
Would you believe us if we said that approximately half of the firms don’t use the basic security best practices? No anti-theft device, backup, or encryption, not to mention other security controls. Even though computer encryption and the implementation of anti-theft technologies are not in the profile of HACKTIFY (for now) – but security awareness and cybersecurity (security testing) is.
So, what is the 3-2-1 security strategy?
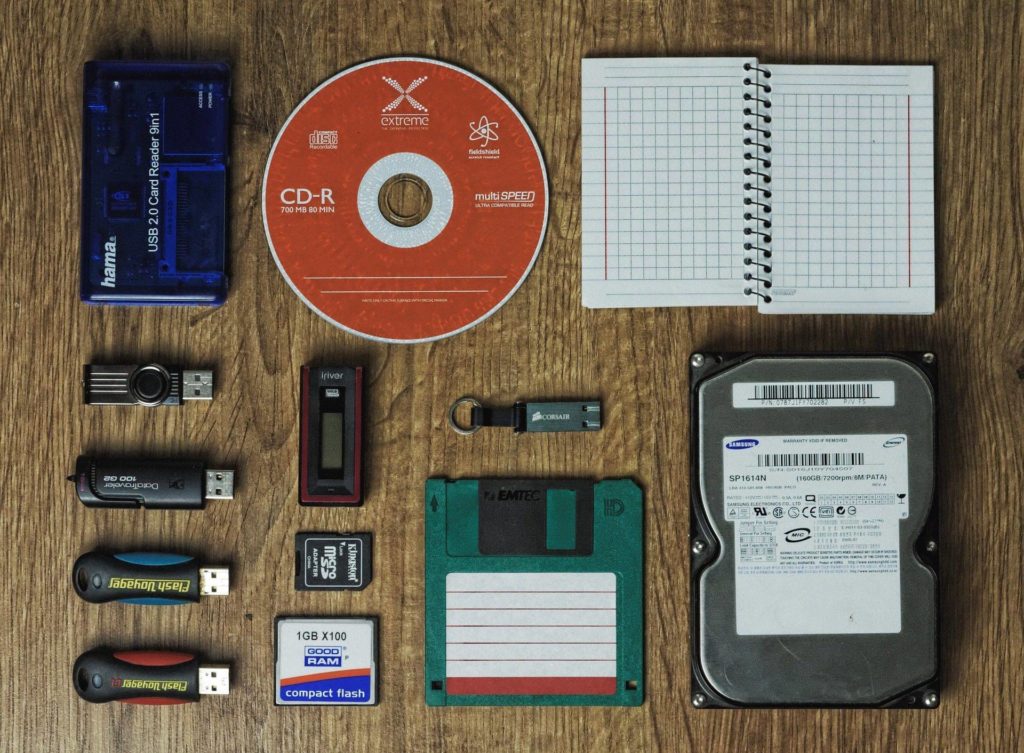
It means that we ought to have at least 3 complete copies of our data – two of which are onsite but on different data carriers; and one, which is offline.
This chart might help:
| 3-2-1 security strategy | ||
| 3 physical copies | 2 copies on additional data carriers | 1 copy offsite |
| 1 live copy (on PC, computer or any endpoint) | 1 copy in the cloud | In the data centre of the cloud providers |
| 2 external backups (on the optical drive, tape, external drive, NAS) | 1 copy on tape, pen drive, DVD, etc. | Offsite storing in a safe, 2-3 hours away from the original location |
Explaining it simply, if you have a folder full of family photos on your computer, then these memories, the photos, the folder itself is a copy. We have an external drive that we use for making backups – you save your data here, in the folder. You have your second copy.
Above these, you can save online, meaning that the file goes to an offshore location, to the cloud, for example. (Before trusting a cloud provider with essential data, take the time to check the service. Use a service which encrypts your data according to the AES [Advanced Encryption Standard] or Blowfish, applies network security practices [firewalls, physically protected hardvers] and ensures that our data will not leak.) You have your third copy here. You leapt into the field of your security and data recovery options.
Why do you need two onsite and an offsite copy?
The point of all saves is that if there is a problem, you can gain access to it relatively quickly to reload the data and files – to have it, at all.
If the hard drive of your laptop, PC or tablet crashes, the majority of your saved data can be reloaded quickly or used on another computer until the original device is fixed or replaced.
Think about it! If you save to the EHD regularly, your exposure to data loss is minimal. Taking the files and data on the device into account, you are already security conscious!
Onsite backup is an amazing thing – “this is the beginning of a beautiful friendship” – but to have a security strategy, offsite backup is just as important.
As mentioned above, onsite backup is good – it can be of service in a crisis. But if the external drive containing the backup is on the same desk or in a nearby drawer, both copies are exposed to data loss (fire, theft, water damage, etc.). Storing the data offline, on an external location – and regularly updating this save – is essential for protecting our data and files.
Is the 3-2-1 strategy the perfect solution?
It is a trite but real approach that a perfect security solution does not exist – but this approach is a wonderful basis for creating a good backup system. Even the US government recommends and supports this technique. Backup is a good investment which pays off when there is a problem. But paying off it handsomely!
The 3-2-1 is a good starting point for saving your files and digital values. If your files are essential, they have value or you see them as capital then they need to be diversificated to limit their exposure. Just in case what you believe to be impossible, happens. What we tried to emphasise all along is that liquidity matters – having onsite and offsite backups offers a wider variety of restoration.
We can only recommend the 3-2-1 strategy as a starting point. Naturally, other methods might work perfectly but our purpose here was to draw those people’s attention to the importance of data loss, who had not thought of the risk of it before.
Naturally, this article was not for firms and maybe the strategy is a strong word but with smaller steps, complex results can be achieved. Committing to an approach like this might do wonders in creating the basis for a firm-wide backup strategy, and restoration plan or in supporting the business continuity.
If you:
Feel vulnerable because you realised that saving is only the tip of the iceberg,
Want to realise what you know on a company level,
Work for an SME and don’t know how to lay the bases of creating a more secure atmosphere,
get in touch with us and we will find the best information security method for you – simply, clearly, without any “bullshit”.
Check out our services and get in contact if you company is in need of
a bug bounty programme (we’ve already written about it here)
vulnerability/intrusion test
GDPR appropriateness or
IT security audit.
Or if you need some assistance with any data security problems.
If we managed to arouse your interest, visit our webpage: https://www.hacktify.eu/en/home/