Frequently asked questions
WHAT IS A BUG BOUNTY PROGRAM?
The bug bounty is a kind of information security testing, in which a company gives reward (i.e. bounty) to the security researchers for the vulnerabilities identified in its services
IS IT RISKY TO HAVE A BUG BOUNTY PROGRAM?
You site can be hacked, can be attacked by malicious intent, if you don’t have a bug bounty program. Moreover, this way you are not aware how your system has been hacked, which vulnerability has been exploited, what data has been stolen, even you have to pay fines in case the data breach gets publicity. The risk of a public bug bounty program doesn’t differ from the risk of a penetration test.
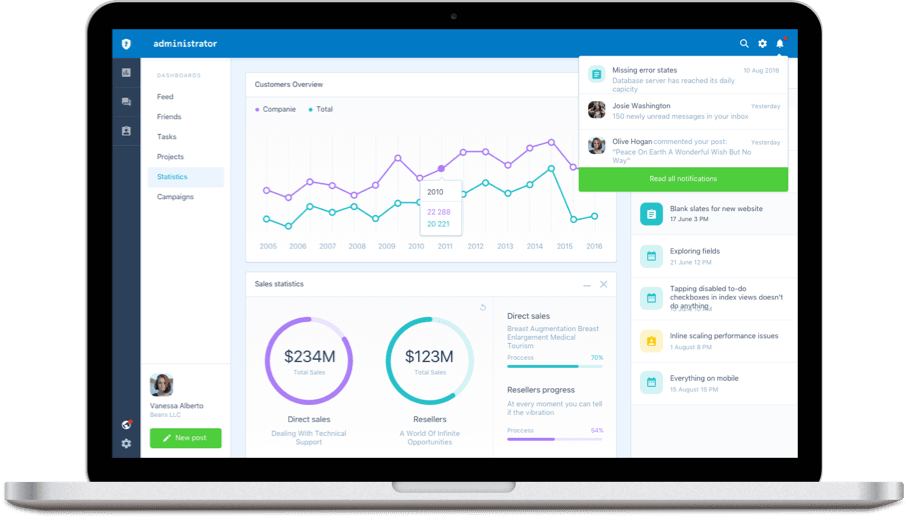
WHAT IS THE PURPOSE OF HACKTIFY WEBSITE?
Hacktify is a bug bounty and vulnerability disclosure platform, which connects companies with security researchers. The program details and the test rules are uploaded to our site. Ethical hackers who sign-up to our webpage can see these and can hunt for vulnerabilities legally and report them through the site
WHAT IS VULNERABILITY DISCLOSURE POLICY (VDP)?
Vulnerability disclosure policy (VDP) is an important document and process for companies that describes how a weakness identified in their services can be legally reported by an individual. If currently this policy doesn’t exist at your firm contact Hacktify! We offer to define this policy for your company and also, we can provide our platform as an interface for this if required.
WHAT BUG BOUNTY PROGRAM TYPES YOU CAN CHOOSE?
Public: A public program is submitted the entire research community registered on the platform. Everybody can find and report bugs through our site.
Private: A private program is submitted to a specific number of researchers, chosen by the client, and is not subject to external communication. Usually these gives a higher reward – and hackers can gain more reputation when participating in such program.
On-site program: Our most discreet program – the solution is tested on the location of the submitter organization by the selected researchers. This type is recommended for products/systems prior production or for hardware and physical devices testing.
WHY SHOULD I ASK SOMEBODY TO HACK MY COMPANY’S SYSTEM?
Every systems have their uniqe complexity. Each components could have different vulnerabilities, moreover newer and newer weaknesses are announced daily which after couple of days can be exploited by malicious hackers. It is better to prevent this and we proactively want to discover and fix these bugs. With this our firm can be more secure and can avoid fines and reputational damage.